

If you can’t take out the battery, it’s never actually off.
Hi guy


If you can’t take out the battery, it’s never actually off.
I don’t use arch, but this applies to my android habits.
Nova has way too many settings now, though.
I use gestures and look&feel and that’s about it. Custom icons here and there. Maybe my app drawer has custom folders, colors, tabs. And maybe my folders use custom gestures, transparency, and colors, and icons.
But that’s it.
On Linux I use the fuck out of custom aliases for basic commands like ls or grep or less - mainly for appearance.
This is the most useful alias to me personally: ls=‘ls -aph --color=always --group-directories-first’


Pooh bear says Think different.


Keep corporations as persons - restore public execution. If a man with the mind of a 10 year old can be executed, so can executives.


ExcludeNodes {US}


It’s not like theres’s an NSA backdoor key called NSAkey in windows or something…


It seems the baddies are way ahead of the curve:


The first two words of the description might provide a hint.?
There is none. This is a personal project. It has been long before brave. The source code is there. All previous results are there. All methods used are there. They make it well known their current employment.
Oh, did I mention you can run the same tests because the whole thing is OPEN SOURCE.?
Well, first, let’s stay on the topic of fact versus your possible issue of possible conflict.
K thx bye.
And yet the results are still fact and brave still isn’t the best.
They’re saying they don’t understand open source at all. They’re saying someone must stop the highly regarded and useful personal project they’ve been working on for years prior to being hired by evil corp (it is because Peter Thiel). They’re saying they don’t know how to read the results of the tests. Etc.
The source code is freely available for you to run all the tests yourself. On any browser you like.
Brave sucks. Peter Thiel can suck the corn out of my shit.
But, the tests and results are still accurate. *based on fresh install and no config changes. (FF can be hardened well beyond what’s shown)
As you can see in the results tor/mull/mullvad/librewolf are basically the best for all around privacy and security.
They’re all based on FF.
Ps: The guy was doing this long before he went to work at brave. (Maybe that’s why they hired him? Hmmm)
PS for all the haters of open source facts : Even librewolf references this site for browser testing.


I use a very old (circa ~2010), very underpowered (6Gb ram because one slot is dead) optiplex 760 with a DP to HDMI adapter to watch movies and live sports on a projector.
I can watch my pirate streamed movie or sports in one window and do other nerd stuff in another no problem.
Running Linux mint-xfce with Firefox, ublock, and containers.
Internet is acquired by tethering one of my old android phones running dnscrypt-proxy and tor (invisible pro), with KDE connect for remote control.


Standard tracking protection and total cookie protection are the default settings. I believe it includes a very minor use of fingerprint tracking protection, but not the resist fingerprint settings.
Privacy.fingerprintProtection (default)
Vs
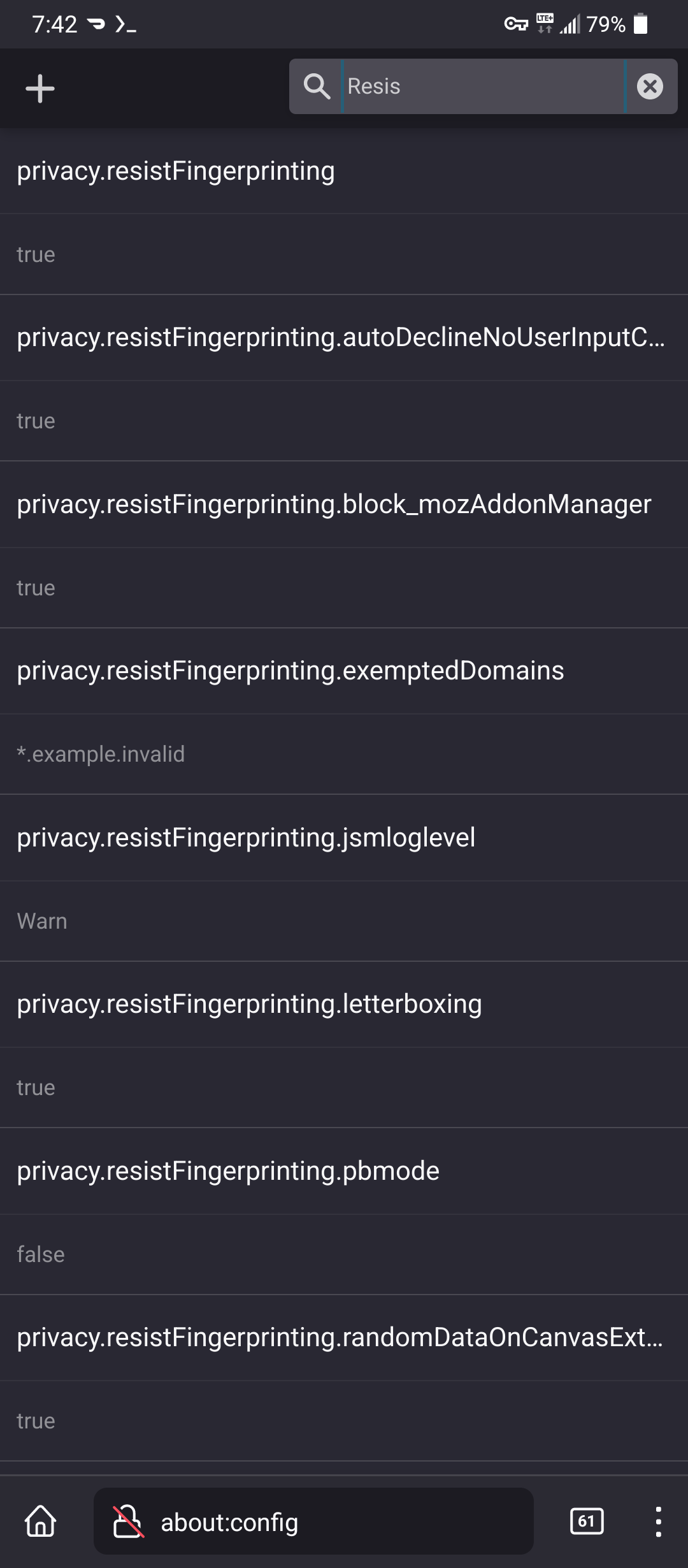
privacy.resistFingerprinting
Resist is the more thorough settings


It has never broken any site i have used.


Carrier unlocked and oem bootloader unlocking are two very different things.
In canada, all phones must now be free of carrier locks, but bootloader unlocking is a pain. The us version of my current phone can be oem unlocked.
Mine can’t.
So, i use a lot of adb/shizuku


They do.
Canvas blocker is one.
If you use firefox (desktop), you dont need a plugin. Go to about:config find privacy.resistFingerprinting
Double click and flip from false to true.
Done.
Go to browserleaks.com/canvas and check your fingerprint.
On android, firefox doesnt have the same option. But, you can use a browser like Mull (a firefox fork) which has all rhe same options as desktop, with the privacy settings of tor browser enabled by default - no fingerprints. (They’ll be fake and new every time)

I’ve never checked the box, when I set address and DNS to manual and add my own routes, not dhcp inherited
ignore automatically provided routesWould seem like a thing to do now?