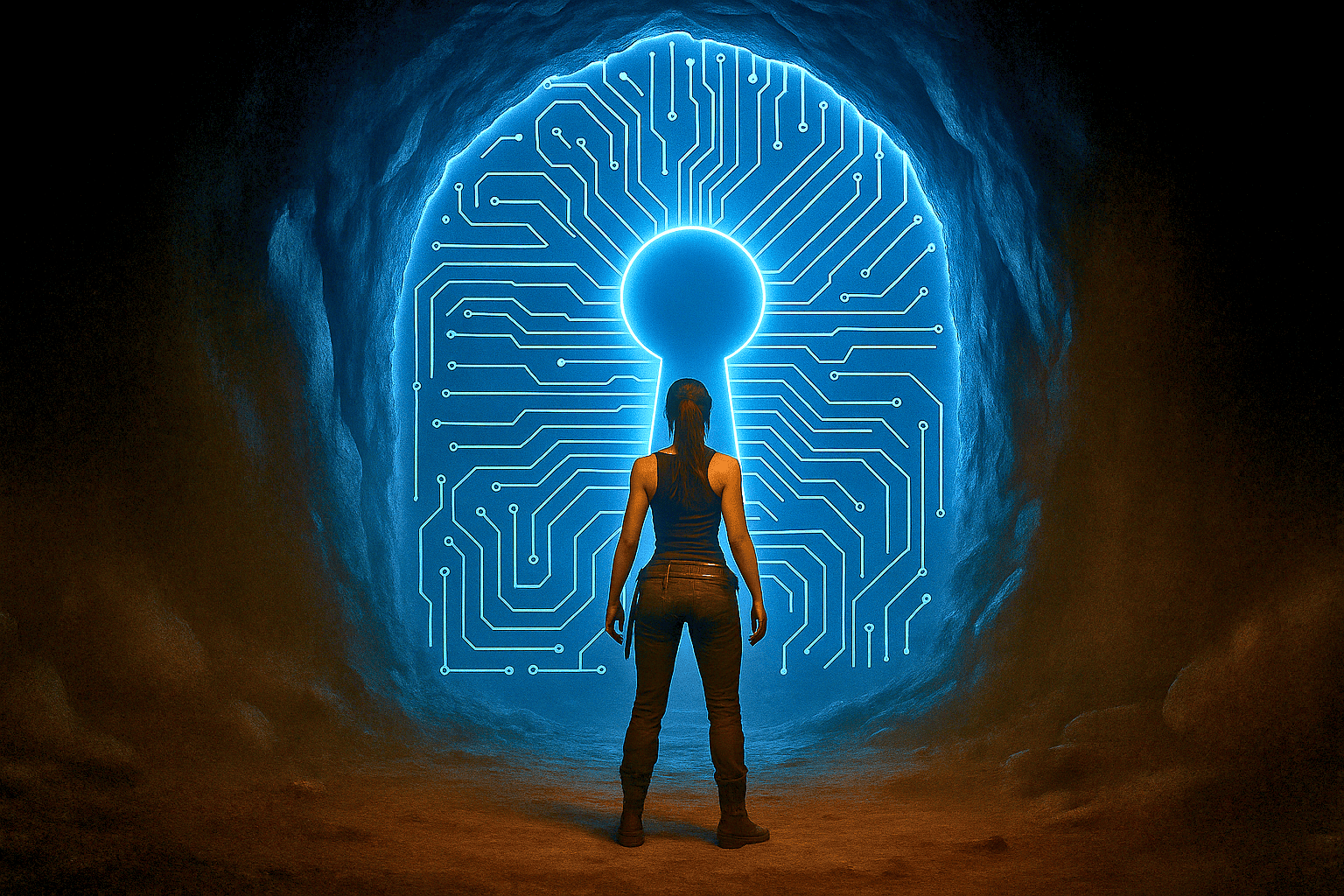
Passkeys are built on the FIDO2 standard (CTAP2 + WebAuthn standards). They remove the shared secret, stop phishing at the source, and make credential-stuffing useless.
But adoption is still low, and interoperability between Apple, Google, and Microsoft isn’t seamless.
I broke down how passkeys work, their strengths, and what’s still missing


The eco-system lock-in makes this a non-starter for me. If I could store the private keys in something like a keepass vault (or that) and do the authentication magic from that I would consider it.
https://keepassxc.org/docs/KeePassXC_UserGuide#_browser_passkey_support
There you go. Local, serverless passkeys in the software of your choice.
I am not dependent on any ecosystem for passkeys. I have a self-hosted vaultwarden instance that works with Bitwarden clients. I create and store my passkeys over there primarily and in my keepass db (which I primarily use for TOTPs) for redundancy. So if either one gets compromised, I can just delete the passkey for the accounts involved in that database.