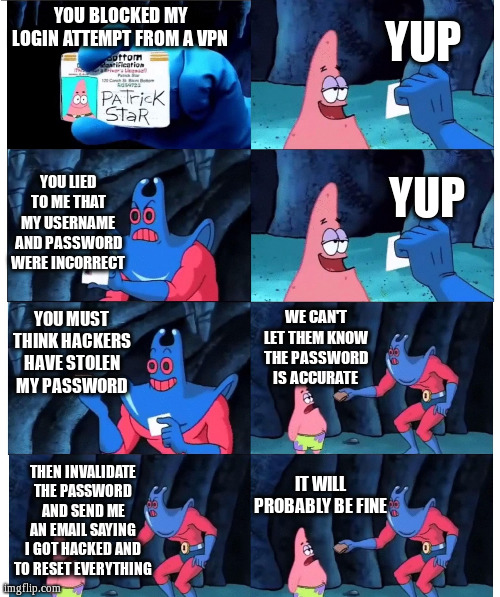
I use ProtonVPN for everything, and I’ve started noticing more and more sites simply blocking me if I try to connect to them through ProtonVPN. As much as it sucks, I’ve more or less become acclimated to having to deal with an increased number of captchas while using a VPN; but I’m pretty angry about being blocked outright. There are at least two broad blocking tactics. First, some sites will say that my network traffic looks suspicious and/or that they simply block traffic from certain IP addresses. But second, and far more maddeningly, some sites tell me that my username and password combo are incorrect when I’m using a VPN. But I know this to be a blatant lie because (1) I use a password manager that auto-fills login forms with credentials that match the domain name, and (2) such sites accept my credentials when I visit them without the VPN connection.
What the hell can we do about this shit? Do I have to run my own VPN to avoid sharing an IP address with other people and thus getting blocked? I really don’t want to do that because I have neither the time nor expertise, and I like that connecting through a VPN provider makes my IP address much less significant. I’m aware that this is connected to the broader conversation about WEI and other methods for determining whether requests are legitimate or not, and I’m sure that businesses of all sizes are reeling from massive increases in bot and AI activity. But solutions that end up punishing legitimate users are not good or valid solutions.
far more maddeningly, some sites tell me that my username and password combo are incorrect when I’m using a VPN
At least they got that far.
There’s a good reason as a web server to block anonymizing VPNs. Turns out the bad guys use them too. Who knew.
That’s an inherent problem with shared connections.
The thing with sites telling you that your login is incorrect is also sometimes intentional, so people trying to brute-force logins won’t realize they’re getting blocked or just that their attempt was incorrect.
And yes, the only possibility is to try a different server that hasn’t been abused, or run your own.
This is what 2FA is for
I don’t know if it even works, but have you considered relying on their Stealth protocol? While its absence on Linux (and Windows) means that you might not even be able to make use of it in the first place, I’m still interested to know if it makes any difference.
deleted
While its absence on Linux (and Windows) means that you might not even be able to make use of it in the first place…
Welp, time to run a proxy server on your phone.
In Termux there’s 4 as far as I am aware. Squid, polipo, privoxy and tinyproxy. I use tinyproxy because it’s pretty simple to set up. Just check the man page.
Alternatively there’s app called “Android proxy server” in Google Play Store, which is the simplest solutionIf you decide to use basic authentication, keep in mind that it’s not encrypted. It’s transported in base64. So definitely don’t reuse passwords, as if you should do that otherwise anyway. If you really don’t want someone else to connect to it, just leave it on localhost and use SSH tunnel.
If you decide to use basic authentication, keep in mind that it’s not encrypted. It’s transported in base64.
You should be using https anyway so that should not matter.
I am talking about basic authentication to HTTP proxy. Useful on multi-user LAN networks.
The real solution is to avoid these sites when possible
But this practice tells you what we all needed to know… They won’t serve u unless they can track you.
Vote with us feet cattle
This is extra maddening with my banking app recently. I even set up split tunneling for it, but it still somehow figures out the VPN. The problem is, it doesn’t let me do ATM withdrawals nor generate one-time virtual cards. Ironically, it still let’s me view full details of my physical card…
So just disconnect from VPN? Oh, not so fast. It remembers that VPN was used at some point, and I’ll have to deactivate the app and then reactivate it without ever connecting to VPN.
Since I have to deactivate and reactivate it daily, immediately when needed, this has led me to decreasing the security by using virtual card reader for 2FA kept on same device as opposed to using physical one and keeping it at home as I used to before this BS.This is what I mean by the physical 2FA card reader:

Yes, that’s the only thing at hand I had to cover the card number :)Lmfao at the arch sticker. Also use arch btw.
Proton VPN advised me to switch to a different server when one is blocked by a website. That usually works for me. I haven’t had the username and password problem though. I think the only sites I’ve had to turn my VPN off for were credit reference agencies.
This has been working for me. Sometimes it’s just the country I randomly connected to and need to pick another random one.
The wrong password is by design. It’s to give the least information to traffic they consider risky.
We need laws that prevent companies from discriminating by how you look. Websites should only be able to deny customers based on how they act. A simple innocent GET from a user with a VPN IP should not be legally permissible reason to deny them.
That thing where they claim the username/password combo is wrong?
That sounds like a really good idea if the site thinks the reason they’re a lot of different lock-on attemps from that one ip is because its a hacker with a list of stolen credentials.
Basically just tell them their list is fake and “go away and stop bothering our customers, please.”
I’ve had this exact scenario happen with my Amazon account. One the one hand its annoying, but on the other I don’t want them to make it easier for someone in another country to order stuff using my account and credit card.
Thats not a good idea because these systems false-positive all the time.
If my first login attempt has the correct username, correct password, and correct totp token, then I should always be let in. That’s literally how auth works.