- cross-posted to:
- linux_memes@programming.dev
- cross-posted to:
- linux_memes@programming.dev
Replying to a 10-year-old tweet is a power move in itself.
I wonder if you string together enough words can it be a valid key?
I would hope so, sentences and words are some of the most secure passwords/phrases you can use
Words are the least secure way to generate a password of a given length because you are limiting your character set to 26, and character N gives you information about the character at position N+1
The most secure way to generate a password is to uniformly pick bytes from the entire character set using a suitable form of entropy
That’s only really true if you’re going to be storing the password in a secure vault after randomly generating it; otherwise, it’s terrible because 1) nobody will be able to remember it so they’ll be writing it down, and 2) it’ll be such a pain to type that people will find ways to circumvent it at every possible turn
Pass phrases, even when taken with the idea that it’s a limited character set that follows a semi predictable flow, if you look at it in terms of the number of words possible it actually is decently secure, especially if the words used are random and not meaningful to the user. Even limiting yourself to the 1000 most common words in the English language and using 4 words, that’s one trillion possible combinations without even accounting for modifying capitalisation, adding a symbol or three, including a short number at the end…
And even with that base set, even if a computer could theoretically try all trillion possibilities quickly, it’ll make a ton of noise, get throttled, and likely lock the account out long before it has a chance to try even the tiniest fraction of them
Your way is theoretically more secure, but practically only works for machines or with secure password storage. If it’s something a human needs to remember and type themselves, phrases of random words is much more viable and much more likely to be used in a secure fashion.
Generally people don’t memorize private keys, but this is applicable when generating pass phrases to protect private keys that are stored locally.
Leaving this here in case anyone wants to use this method: https://www.eff.org/dice
We are talking about RSA though, so there is a fixed character length and it isn’t meant to be remembered because your private key is stored on disk.
Yes the word method is better than a random character password when length is unbounded, but creating secure and memorable passwords is a bit of an oxymoron in today’s date and age - if you are relying on remembering your passwords that likely means you are reusing at least some of them, which is arguably one of the worst things you can do.
You didn’t have to call me out like that.
That’s why you need lots of words. (6) If you combine that with a large word list it gets very secure.
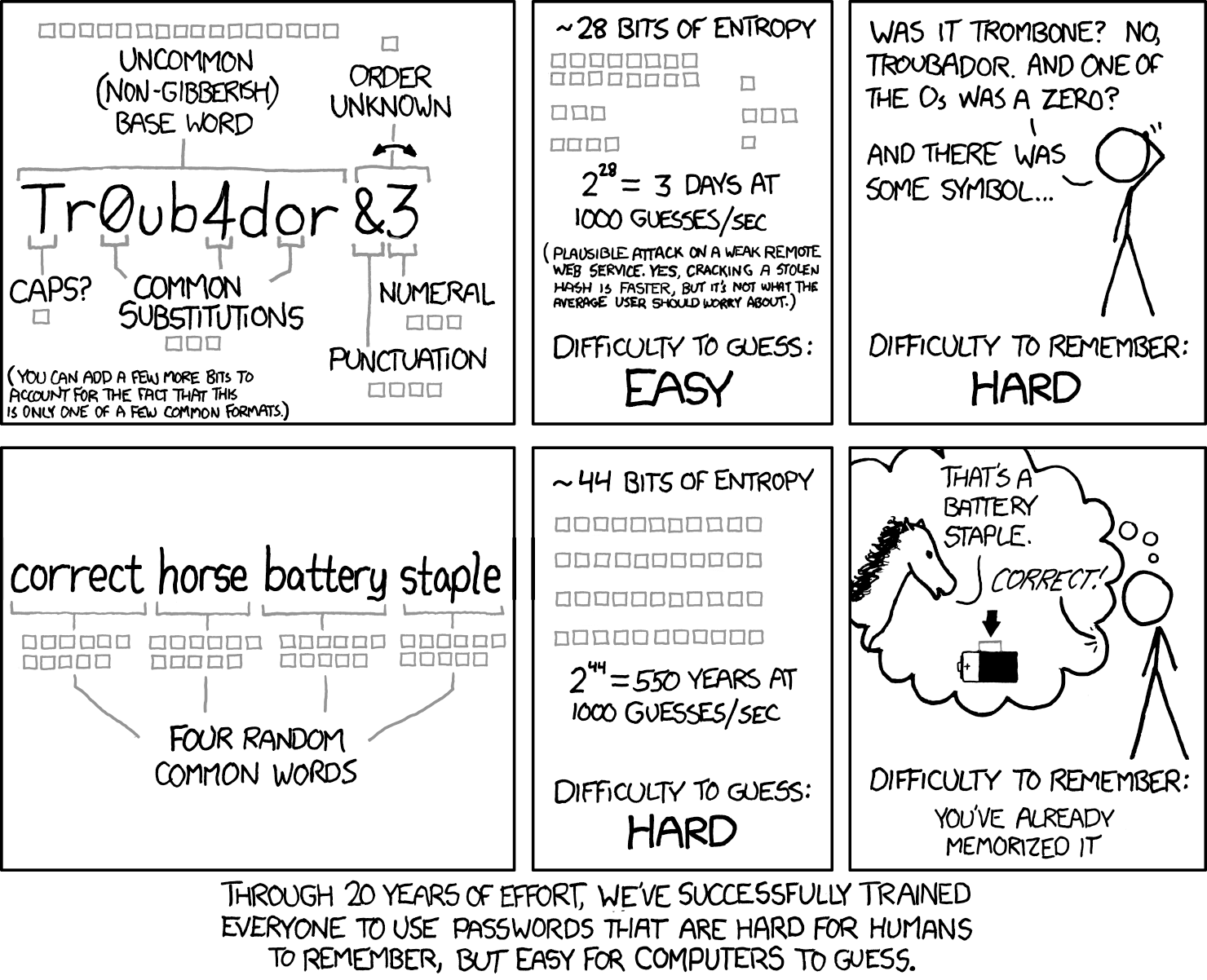
so you are saying 44 bits of entropy is not enough. the whole point of the comic is, that 4 words out of a list of 2000 is more secure then some shorter password with leetcode and a number and punctuation at the end. which feels rather intuitive given that 4 words are way easier to remember
The part where this falls flat is that using dictionary words is one of the first step in finding unsecured password. Starting with a character by character brute force might land you on a secure password eventually, but going by dictionary and common string is sure to land you on an unsecured password fast.
Even if an attacker knew that your password was exactly four words from a specific list of only 2048 common words, that password would still be more secure than something like
Tr0ub4dor&3https://www.explainxkcd.com/wiki/index.php/936:_Password_Strength
If the attacker search for your password specifically then xkcd themself posted the reason why it wouldn’t really matter
https://www.explainxkcd.com/wiki/index.php/538:_Security
If you’re doing blind attemps on a large set of users you’ll aim for the least secured password first, dictionary words and known strings.
That’d why words are from the eff long word list and there are 6 words
While this comic is good for people that do the former or have very short passwords, it often misleads from the fact that humans simply shouldn’t try to remember more than one really good password (for a password manager) and apply proper supplementary techniques like 2FA. One fully random password of enough length will do better than both of these, and it’s not even close. It will take like a week or so of typing it to properly memorize it, but once you do, everything beyond that will all be fully random too, and will be remembered by the password manager.
then someone uses a dictionary attack and your password gets cracked within minutes
see, you didn’t get the whole comic. 4 words out of a dicitionary with 2000 words has more combinations then a single uncommon non gibberish baseword with numeral and puction at the end. as long as the attacker knows your method.
a dicitonary attack will not lower the entropy of 44 bits, thats what the comic is trying to say
It’s assymetric crypto. You’d need to find a matching public key. Or it’s just some useless characters. I suppose that’s impossible, or what we call that… Like take a few billion years to compute. But I’m not an expert on RSA.
Public keys are derived from the private key. The asymmetric part is for communication not generation. Afaik
I’m pretty sure the cryptographic parameters to generate that public key are included in the private key file. So while you can generate the other file from that file, it’s not only the private part in it and you can’t really change the characters in the private key file. Also not an expert here. I’m fairly certain that it can’t happen the other way round, or you could impersonate someone and do all kinds of MITM attacks… In this case I’ve just tried changing characters and openssh-keygen complains.
The surprised man in the middle
Reddit did it in reverse for Tor
this is gold yet I don’t know anyone who would get it that I can share it with
I just shared it with a bunch of people while also telling them that I didn’t care if they didn’t get it and I wasn’t going to explain it.
They’re used to this.
Edit: 2 of them got it. That’s pretty good for me. I’ve played to smaller crowds.
I shared it to the memes group at work, as a developer
That’s why we come to the internet. Real life people suck.
That’s why I have a sister studying cyber sec 😎
I have exactly one person and they loved it.
If you had to explain it, how would you?
Burst a kidney please help
It’s sad that I can’t find anyone to share this with.
I have literally one friend who would get this, and I try not to bombard him with memes, as I can tell it gets on his nerves sometimes, even when he thinks it’s funny.
I’m in your exact camp.
I share these with friends who might not get it. It’s like a UDP joke
ACK
NAK
␆
I genuinely LOL’d at this thank you OP.
While the joke is funny, what is the context? Why did she post the original tweet in the first place?
It’s lady gaga.
If you’ve followed her at all, even indirectly, this is NOT the weirdest thing she’s done, and bluntly, the weirder stuff wasn’t justified (to the public at least).
I’m not trying to throw shade at Gaga at all. Lady, let your freak flag fly all day long. You don’t need my permission to do it, but if you want it, you got it. Weird isn’t bad, it’s just weird.
IMO, at this point, gaga doesn’t need a reason to be weird.
lol